2 Ways Your PayPal Account Could Be Wiped Out
Weak Passwords Can be Very Expensive
2 Ways Your PayPal Account Could Be Wiped Out
Most cybersecurity professionals spend some time on the dark web. We do this for research and to understand what we should expect from bad actors on the internet. I just recorded a video for my company’s website explaining how weak passwords, and probably some phishing, likely lead to Netflix accounts being compromised and sold on the dark web. You can watch that video here.
The dark web is the black market on the internet. You can purchase almost anything including hitmen and drugs.
What you see more of though is stolen credit cards and compromised PayPal accounts.
As I was doing some research for the Netflix video I stumbled on another Onion site. Onion sites are websites on the dark web. Typically they are not found on Google or the internet you’re familiar with. Think of them as the dark alley you normally would avoid because that’s where all the bad guys hang out and all the illegal activities take place.
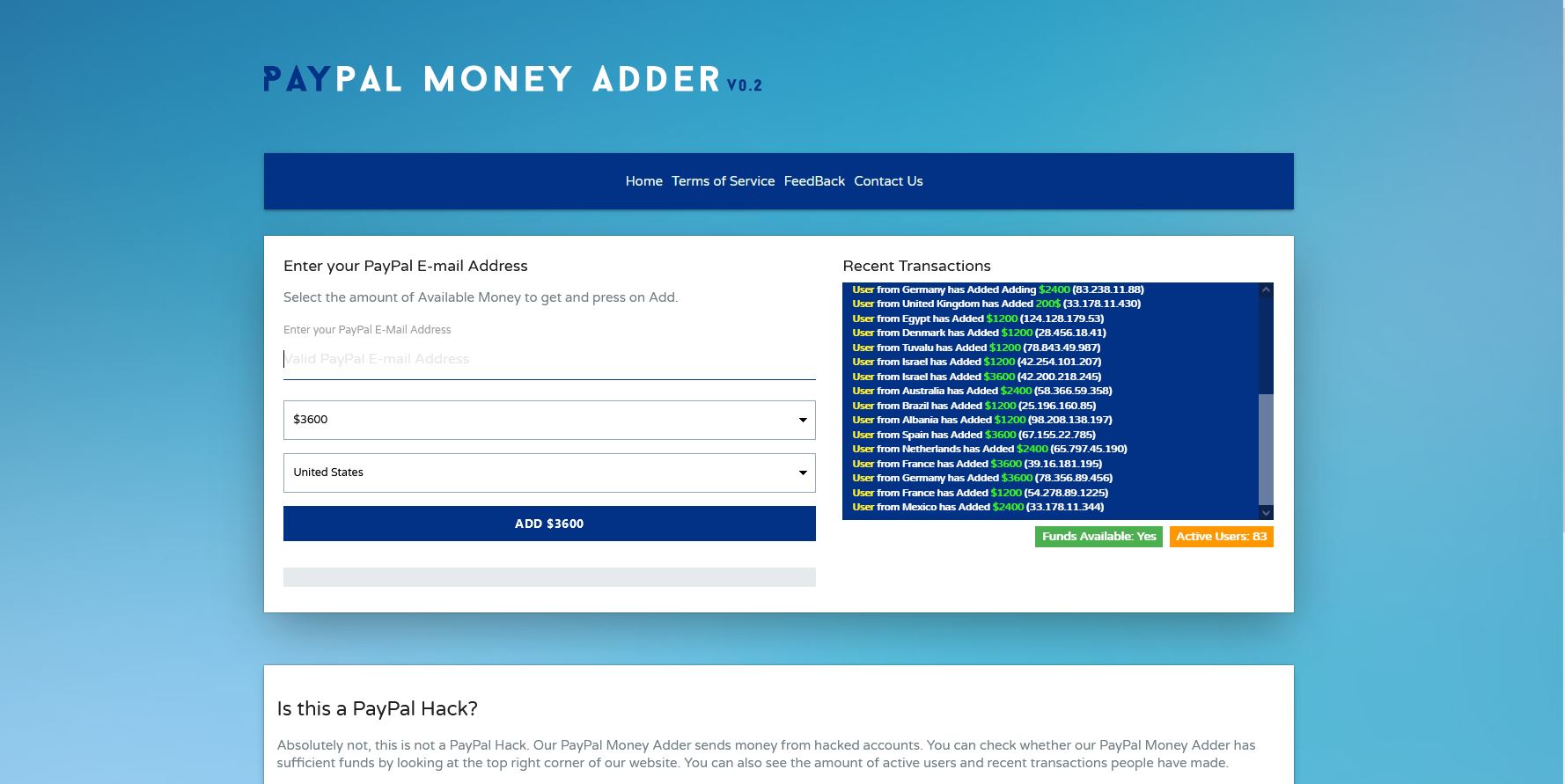
The Onion site I stumbled on is called PayPal Money Add v .02.
This site purports to send money to someone’s PayPal account. The way it works is you choose how much you want to be deposited into your PayPal account and they charge you 10% of that amount. So if I wanted to have $1200 deposited into my PayPal account I provide the email address associated with my PayPal account, and the country I am in. I then have to pay $120 in BTC (Bitcoin).
Dark web transactions usually use cryptocurrency because it’s harder to track, and harder to recover.
They even mention how they will send it as a gift to avoid potential issues with PayPal. They also mention that this is not a PayPal hack but rather they are sending money from hacked PayPal accounts.
Read that again. They didn’t hack PayPal. They hacked user accounts on PayPal.
How Does A PayPal Account Get Hacked?
Like most accounts that are compromised, it was either weak password policies or some form of social engineering, probably phishing. Here are 2 Ways Your PayPal Account Could be Wiped Out.
Weak Password Policies
Breaches happen every day. Major websites are breached all the time. Here is an example of how a password I used to use wound up on the dark web. In 2012 6.5 million LinkedIn account passwords were stolen. Those credentials eventually found their way to the dark web. The culprit was eventually caught and received an 88-month prison sentence. Then in 2016 LinkedIn discovered that an additional 100 million usernames and passwords were stolen in the 2012 breach.
All of those credentials are still on the dark web today. They can be purchased, and are sometimes available for free.
My account was one of the 106.5 million accounts that were breached. The email address and password I used at the time are still on the dark web. I no longer use that email account for anything, and I do not use that password or any variation of it at all.
When your credentials are compromised during a data breach they are almost always placed on the dark web and sold to different groups. They can be used to breach accounts, business networks, launch ransomware attacks, or steal someone’s identity. Credentials are typically sold for a few dollars at most. In this scenario, the person(s) with the credentials will then test those credentials on various platforms, applications, and programs to see what works. PayPal is one of the more popular applications to test for attackers.
Imagine a list of 106.5 million credentials and a script that tries each one on PayPal and returns a log file of which ones worked. And that’s from just one breach.
Weak passwords wreak havoc all the time. The Ring Camera breach in 2020 was caused by weak, reused account credentials. In this blog post, we talked about how a weak password led to a BEC scam.
Whether in business or personal life, weak password policies can be detrimental to your financial stability.
Phishing
You received a text message from PayPal stating you need to confirm a recent transaction for $750. This caused you to panic a little so you clicked on the link in the text message which took you to the PayPal login page.
You proceed to log in with your credentials but keep receiving an error message. You think to yourself maybe it’s because you’re on your phone so you go to a computer and try again. During the time it takes for you to do this someone else grabbed your credentials from the PayPal phishing site you just tried to log in to. They emptied your account in just a few minutes. You were phished via text message, also known as SMishing.
The Human Element
In both instances, attackers preyed on human vulnerabilities. That is they took advantage of our own lack of understanding (how breaches occur), desire to take shortcuts (reuse passwords), or fear of financial loss. When I say people are the weakest link in any cybersecurity plan it’s not meant to be an insult. It’s meant to help you understand. It’s meant to educate and prepare for potential social engineering scams.
People usually are unsuspecting of scammers, especially under the guise of authority or assistance. We just want simplicity and all of these complications confuse us and raise our stress levels. Confusion, stress, and fear sometimes lead to disaster.
Final Thoughts
PayPal accounts are a very popular target. Financial accounts in general are appealing to attackers and thieves. Passing money from one PayPal account to another, and collecting Bitcoin in return, means the attackers are taking on very little risk. The risk is all on the PayPal account that receives the money.
To protect yourself and your financial accounts ensure you are using a complex password policy, Two-Factor Authentication (not through text messaging), and always think before responding to a message that invokes a strong emotion.

 The Human Element
The Human Element
Leave a Reply
Want to join the discussion?Feel free to contribute!